Reviving an old dead or bricked Buffalo Linkstation
Note: The HS-DHGL Linkstation and Terastation were launched back in 2007.

Background
Buffalo produce a range of NAS (Network Attached Storage) products. With the (old) examples covered here a characteristic of their approach is the actual firmware for the units is stored on the hard drive (single disk unit) or drives (RAID boxes) within the product.
An obvious consequence of this is that, should a drive or file get corrupted, you can end up with a box that just sits there beeping at you and refusing to run. Similarly, should you decide to replace that 250GB drive by a 2TB drive (which I did) you're in a similar situation.
Obviously there must be a way out of this, and in the case of products like the early Linkstation Live and Terastation products it is a two stage process.
I originally drafted this description some years ago (luckily!). I've just dug out an old Linkstation (HS-DHGL) fitted with a 2TB drive which, when powered up, just sat and beeped at me. The original online resources I used before seem to have vanished but my half-drafted words from four years ago and an old USB pen drive with the right software still on it let me resurrect it.
Whilst the HS-DHGL dates from 2007 they still do work and I'm sure there are others lurking in the backs of cupboards that might yet still see the light of day. In my case they are just acting as a network resource where I can backup my various main systems to. They can also store stuff that is only rarely needed.
So here's my guide of how you can bring them back to life.
The Recovery process
There is obviously some limited firmware stored in flash memory on the circuit board within the Linkstation/Terastation that normally boots the operating system off the internal hard drive - and produces the beeps if it can't find it.
It has a secondary mode that can be invoked where it downloads alternative recovery software from the network and then executes that.
This in turn is used to allow the final firmware to be downloaded within a normal Windows/LAN environment and stored on the Linkstation/Terastation.
Looking at each step in turn:
- To get the Linkstation to come up in "Recovery Mode" you press and hold
the reset button on the back whilst the unit is powered up. Note by "powered up" I mean
switching on the power from the mains socket on the wall. The actual 'on' button on
the unit is just a polite request to the already running firmware to either power up
the disk drives and start running or to power them down and go into a state of
suspended animation.
As the Linkstation Live (HS-DHGL series) used in this example has no on/off power switch on the back you have to be holding the reset button down when you either: (a) Switch on power at the wall socket, or (b) Push the figure-of-eight mains connector into the socket on the back of the unit. Another pair of hands can be a help when you're doing this. You should keep holding the reset button down for a few seconds to allow the on-board firmware time to start up and notice that the button is being pressed.
At this point the firmware knows it has to switch to recovery mode if it encounters any issues whilst it is starting up. With the HS-DHGL, having got external power applied, you then have to press the power button on the front to get it to turn on the LEDs and start doing something.
- When it starts running, although you've flagged you want recovery mode, it still
seems to go through the normal start up process which ends with the error beeps.
However, at this point Recovery Mode kicks in. It sets its IP address to 192.168.11.151
(I have also seen 192.168.11.150) and then it requests a file from a TFTP server at
IP address 192.168.11.1. The recovery disk includes three files: u-boot.buffalo,
initrd.buffalo and uImage.buffalo. I assume that it may depend on the
exact model being re-imaged as to which files are requested. In my case, with one of my
Linkstations, it only asked for uImage.buffalo.
Assuming a TFTP server responds it automatically downloads these file(s) into its memory and starts it running. (Note: From what I've seen it does not write this interim firmware to the hard disk).
- At this point, with the stage 2 bootstrap software running, it is now in EM mode. (EM standing for Emergency Mode(?) ). Here it will use DHCP to request an IP address from your local DHCP server and will appear on your local network albeit with no NAS features as yet.
- You then can then switch to your main PC and run the standard Buffalo firmware updater (LS_UPDATE.EXE) to download the latest firmware to the unit.
What you need
You need two sets of files to recover your unit - the standard firmware and the tftp boot files. You should find the standard firmware on Buffalo's website: http://www.buffalo.com for the US and http://www.buffalo-technology.com/ for Europe. This will be a zip file that will contain the firmware files and the (windows) updater program.
Locating the recovery TFTP files is more difficult but with a bit of work with Google you should be able to track them down. In that zip file (or self-extracting exe) there's also a Windows executable which is a TFTP server.
To save you the trouble here's what I tracked down:
That file is the complete package which is a self extracting compressed archive.
If you are wary about downloading random executable files from the Internet the three files below are the various firmware files that are included in the compressed archive.
Finally there's the issue of how you deal with the first step described above.
The first time I did this a spent a while reconfiguring my main Windows machine to run with an IP address of 192.168.11.1 and using the supplied TFTP server software. It took an inordinate amount of time to do this, a lot of the time fighting Windows who insisted on using some random IP address rather than the 192.168.11.1 that I thought I had selected.
I subsequently came up with what I regard as a very much simpler approach (for me at least) that means you don't have to do anything to your main machine. It's just a matter of briefly booting a small Linux system from a USB pen drive. In my case I used a separate PC (actually a Thin Client) for this but it could just as easily been a laptop or my main PC.
The TFTP server
For this I used Tiny Core Linux, a small and neat Linux distribution that I'm familiar with and have used for a number of projects. In this case the beauty(?) of the approach was that all I needed to do was:
- Download the latest Tiny Core ISO.
- Use LiLi to create a bootable pen drive with Tiny Core Linux on it.
- Copy the two buffalo files to the pen drive.
- Make a couple of simple edits.
- Boot into Tiny Core.
- Type a couple of commands.
- Power up the Linkstation.
That's it.
There's also a side benefit. The network monitoring application wireshark is also available (this is for Tiny Core 11.x). Installing this as well lets you see what's happening on the network which can be a help if things aren't quite working to plan.
Note: Modern ethernet hubs are switches. In the olden days they just copied all incoming traffic on a port to all the other ports on the hub. These days they are more intelligent and only copy the incoming traffic to the right outgoing port. (Obviously any broadcast message still goes to all ports). Running Wireshark on your TFTP server guarantees it will see all the traffic to/from it. If your network monitoring software is running elsewhere you'll need to use a managed switch that you can configure to copy all traffic passing through it to a designated port. A Netgear GS108T is an example of such a switch.
Here's the outline of what to do:
- Use a tool such as LiLi (Linux Live USB creator) to install the latest version of Tiny Core onto a USB pen drive.
- Copy the necessary files to the pen drive. I copied them to buffalo/HS_DHGL.
- Boot the pen drive and check that it works.
- Note which device the USB drive is when booted on your target hardware. Using a command like dmesg | grep sd can help you see what drives the system has found and how it has named them. In my case, where I used a system with a single existing disk drive, the USB pen drive appeared as /dev/sdb.
- If you intend to use Wireshark use the App browser to download Wireshark and Xorg. (Note Wireshark does not run under the Xvesa driver, you need Xorg).
- Edit the startup parameters to include nodhcp (In my case I created another entry in syslinux.cfg file and added nodhcp to the APPEND line.)
- Create a shell script in the root directory of the pen drive. I named mine recovery.sh.
#!/bin/sh sudo ifconfig eth0 192.168.11.1 sudo echo 69 dgram udp nowait root tftpd tftpd /mnt/sdb1/buffalo/HS_DHGL >/etc/inetd.conf sudo inetd
- Boot the nodhcp option.
- Open a console and run the shell script /mnt/sdb1/recovery.sh
- Boot your Linkstation
At this point you can check that all has happened correctly by using a browser on your PC to logon to the admin page of your router. Somewhere you should find an option to view a list of connected devices. Hopefully you'll see the Linkstation (or Terastation) there in the list. (There's also the possibility that it might be showing as 'unknown' depending on the sophistication of your router's software).
Update
Run the updater software from Buffalo.
This time when I went through the procedure the Buffalo Windows updater failed after a while with an error message ACP_STATE_FAILURE. I tried a few times with some other tweaks but to no avail. Eventually I just ignored it and found out that the Linkstation had in fact been updated and, when rebooted, ran quite normally.
The Aftermath
One final hurdle is that if you point a browser at your resurrected Linkstation you find that it has reverted to Japanese:
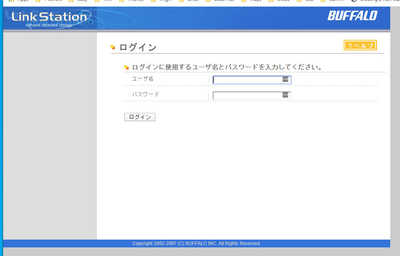
Actually the first time I visited this page the top right of the window was overlayed with other rubbish. The left-hand end of the top entry box was just visible. This is the logon page so you need to enter the default values of admin and password.
This takes you on to:

Here you need to click on the second item in the left-hand menu. This gets you to:

At the bottom of the page there are two selection boxes. You need to set the top one to English (or whatever your language of choice is) and the lower box to CP437:

Then click on the button at the bottom left to save the result. Your selected language will be used the next time you login.
Using your old NAS
NAS products of this era use the SMBv1 network protocol. A significant vulnerability was discovered in this protocol in 2016(?) and since then the SMB protocol has moved on to v2 and v3. Due to the significant vulnerability in the v1 protocol Microsoft now disables it and you may find that your newly rebuilt NAS box is invisible to your Windows PC. Luckily you can turn support for SMBv1 back on via the Windows Control Panel or turn windows features on or off. Google offers various ways to get to this setting.

This is one of those infuriating situations where old hardware can still be useful but the lack of a simple software update gets in the way.
Any NAS box which reached end-of-life before 2016/2017 almost certainly is using SMBv1. I have some old Western Digital 'My Cloud' and 'My Book' devices which are in the same boat.
Note: If you are enabling SMBv1 on your home network you need to be confident that it is properly firewalled from the internet - a job normally performed by your cable modem (or whatever). Mr Google says:
To block SMBv1 vulnerabilities, you should block TCP ports 139 and 445 and UDP ports 137 and 138 at your network boundary.
